Introduction:
In the rapidly changing world of cloud computing, AWS IAM plays a critical role in making sure that only the right people have secure access. IAM, which stands for Identity and Access Management, gives users the power to control who can do what, ensuring that only the necessary permissions are given out. It's more than just confirming who you are – IAM also provides a strong way to safely share and work together across different accounts. At its core, IAM policies are really important because they define what actions are allowed, making sure everything stays secure. In this blog, you will learn more about the significance of AWS IAM and how it contributes to maintaining robust cloud security.
Now, Let's Get Into the Story:

Real-Life Example:
Think about a bank with lots of services available. Imagine it's like a place where you can ask about your accounts and money stuff. There's also a part where bank workers do their jobs, and then there's a super secure area where they keep important papers, records, and money. To make sure things run smoothly and securely, the bank follows a detailed plan.
First, only people who can prove they belong, like having an account, can come in. When someone gets inside, the bank checks what they're allowed to do based on their job – if they work at the bank or are a customer. Depending on this, they're allowed to go to certain places and do specific things. This careful process keeps things organized and stops the wrong people from getting into sensitive spots or doing things they shouldn't.
This whole setup acts like a shield for the bank. Without it, there could be problems with security, maybe even things happening that shouldn't. So, the bank makes sure only the right people can get to certain places and do certain jobs. This happens by confirming who they are (authentication) and deciding what they can do (authorization). These two things work together to keep the bank safe.
Connecting the Story to IAM Service:

Now, let's make this story simpler by thinking about a DevOps engineer working with AWS. Imagine this engineer is setting up an AWS account for a company called Example.com. The worry here is that AWS doesn't have strong security right now, which could lead to problems. It's like having a key to important rooms with no locks. That means anyone, on purpose or by accident, could mess things up or delete important stuff.
To fix this, AWS has a thing called IAM. Imagine IAM as a guard that gives special keys only to the right people. Instead of everyone having a big master key, this guard (IAM) makes individual keys for each person, each one letting them do different things. This keeps things organized and makes sure people can only do what their job needs. It's like giving someone a key to read a book but not letting them rip out pages. IAM makes sure things stay secure and in order. The story hints that we'll learn more about this later.
Understanding IAM's Building Blocks:
1) Users:
Imagine making a new person part of the security plan. It's like giving them a badge that lets them into a building. When someone joins a company, they get a special 'badge,' which is like a user profile. This profile lets them use cloud services in AWS. But it's not just about getting in – it's about saying what they're allowed to do once they're in. This is where policies come in.
2) Policies:
Policies are like rules that say what a person can do in the cloud. These rules decide what they can change, see, or use. Without policies, someone might get in but not be able to do much. Policies make sure people have the right permissions to do their jobs well. It's like giving someone keys to some rooms, but only letting them open certain doors.
3) Groups:
Imagine lots of people coming and going. Setting up access for every person can be a hassle, right? That's where groups come in. Think of groups as categories that help manage access. As a DevOps engineer, you can group people as 'developers,' 'QA engineers,' 'DB administrators,' and more. Instead of giving each person access one by one, you give access to groups. So, when a new person joins, you just put them in the right group – it's like giving them a membership card.
4) Roles:
Roles work a bit differently. Imagine an app needing access to a cloud service. It's not a person, but it still needs to get in. Roles act like temporary passes for this. For example, if an app needs data from a cloud database, you create a 'role' for it. This role lets the app in for a short time and specific tasks. It's like lending your friend your Netflix account for a movie night – you trust them, but you set limits.
By understanding these basic ideas, you'll be better at using AWS IAM and making your cloud setup more secure and smooth.
Let's Do a Hands-on :
Exercise :
As you probably know at this point, it's not recommended to work with the root account in AWS. For this reason, you are going to create a new account that you'll use regularly as the admin account.
Create a user with password credentials
Add the newly created user to a group called "admin" and attach to it the policy called "Administrator Access"
Make sure the user has a tag called the key
Roleand the valueDevOps
Solution :
Go to the AWS IAM service
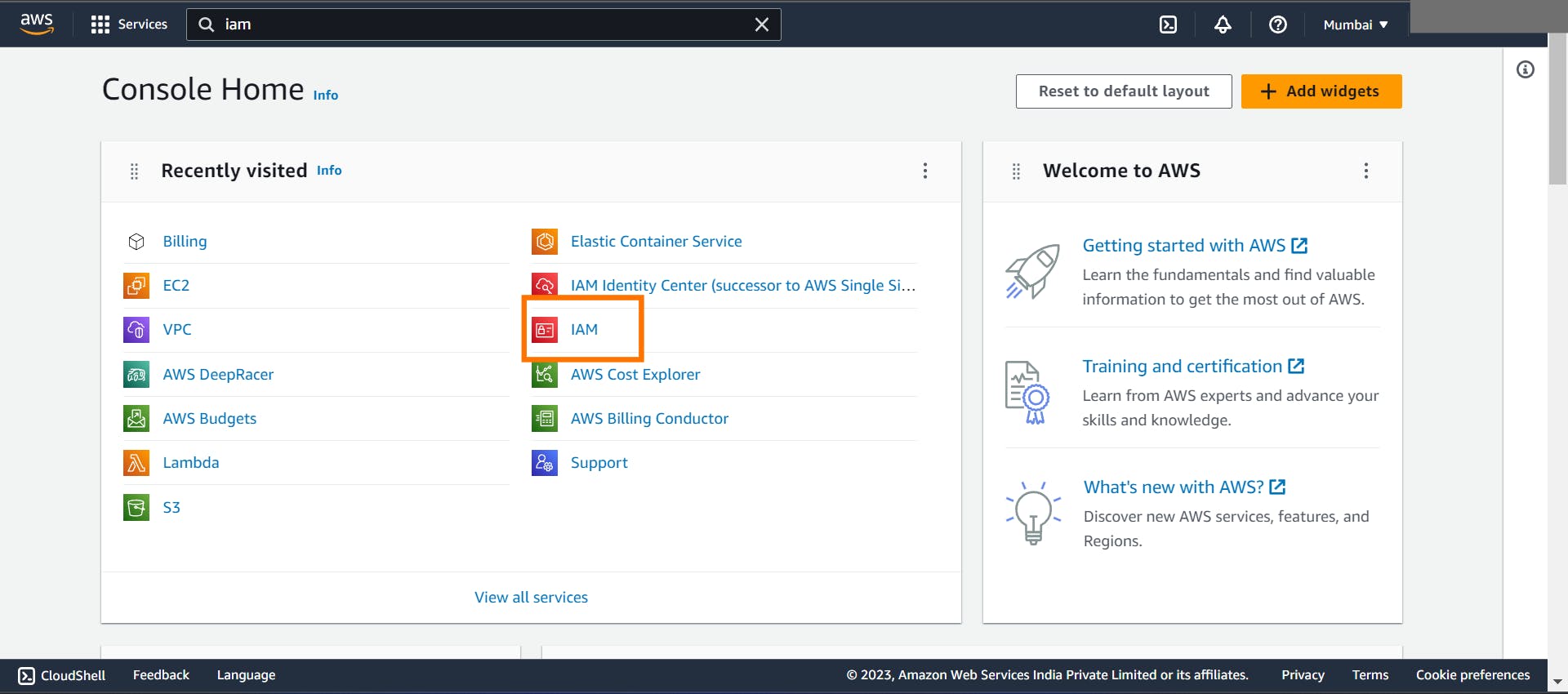
Click on "Users" in the right side menu (right under "Access Management")
Click on the button "Add users"

- Insert the user name (e.g. Kelvin)

Select the credential type: "Password"
Set the console password to custom and click on "Next"

- Click on "Add user to group"

Insert "admin" as the group name
Check the "AdministratorAccess" policy and click on "Create group"
Click on "Next: Tags"

- Add a tag with the key
Roleand the valueDevOps
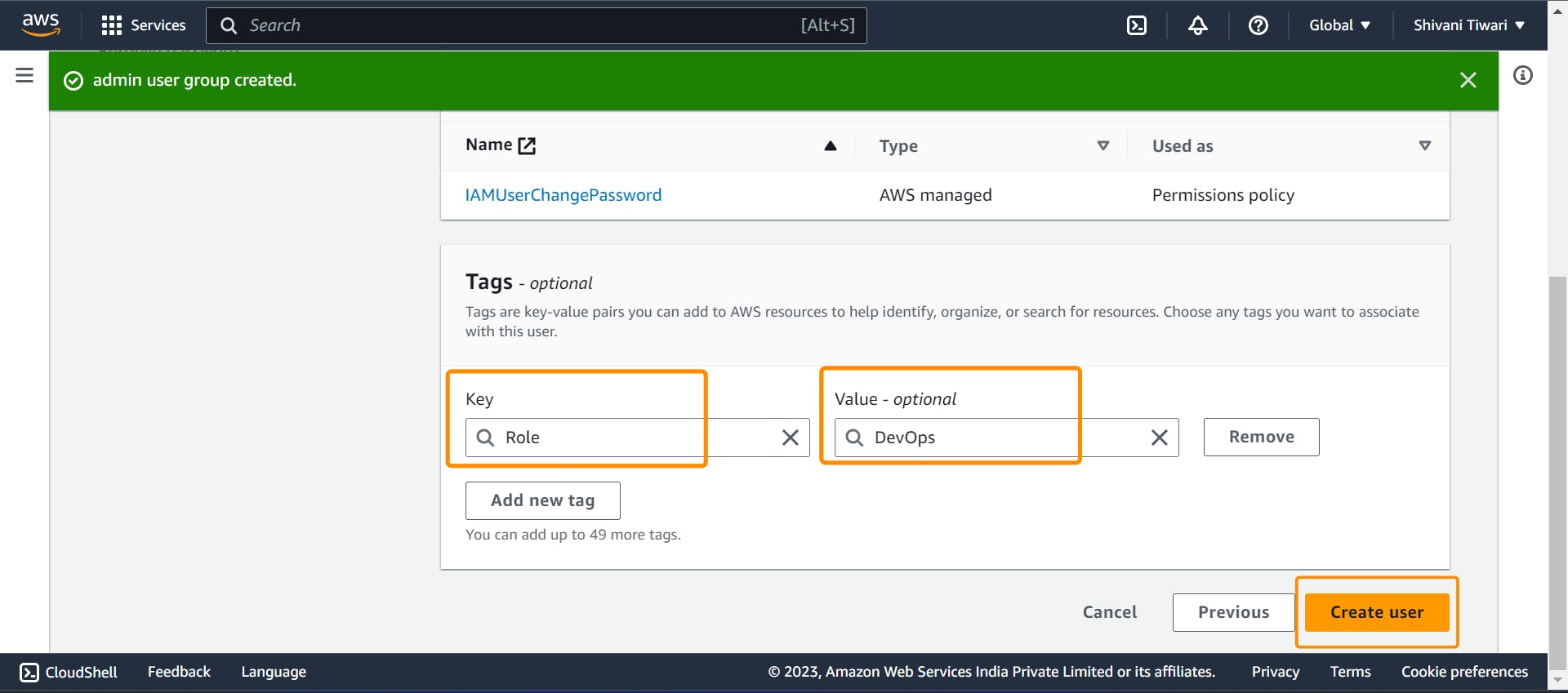
- then create on "Create user"

Conclusion :
To sum up, AWS Identity and Access Management (IAM) is like a guard for cloud setups. It uses users, policies, groups, and roles to make sure access is secure. Just like the bank controls who goes where, IAM gives out special keys, stopping chaos and problems. Policies shape access, groups manage users, and roles add security – all similar to controlled lending. Knowing these ideas helps you use AWS IAM better, making your cloud secure and efficient. The exercise shows how important IAM is by helping you create users and give them permissions, showing how to use IAM in real situations for better cloud security.